The security team at CWS has been working to assess the impact for our customers in the wake of April 7th’s disclosure of CVE-2014-0160, known colloquially as Heartbleed. We join nearly every service provider on the Internet responding to this critical vulnerability in OpenSSL’s handling of heartbeat packets and conducted a comprehensive security review on 4/8/14 in response. We also believe it’s important to let you know what we know, what you need to do and where you can find additional help from us.
After our investigation there is no evidence that any user credentials or account credentials on CWS networks were compromised. All affected systems at CWS were patched as of 11:37pm on 4/8/14. However, we recommend our customers who utilize SSL security take some additional steps to ensure the security of their websites and applications. First, all SSL certificates have been (or will be) re-keyed automatically by CWS security personnel. Second, if your website utilizes SSL (https://) and has end user authentication we are recommending all end users change their passwords as an extra precaution.
Finally, because this vulnerability affects as much as 60% of servers on the Internet, CWS is in the process of testing all third party vendor services for potential vulnerabilities related to CVE-2014-0160. Now would be a great time to change all passwords that you use on the Internet.
We hope this answers your questions about the impact of CVE-2014-0160 on your website. Feel free to reply this email to reach our Customer Support team with follow up questions.
For more information about this vulnerability, please visit:
* The Heartbleed Bug: http://heartbleed.com/
* OpenSSL’s official advisory: https://www.openssl.org/news/secadv_20140407.txt
* Lifehackers Heartbleed Breakdown
* AWS Security Bulletin page: https://aws.amazon.com/security/security-bulletins/
Thank you,
CWS Security

.jpg?t=1533315998368) How-To Articles
How-To Articles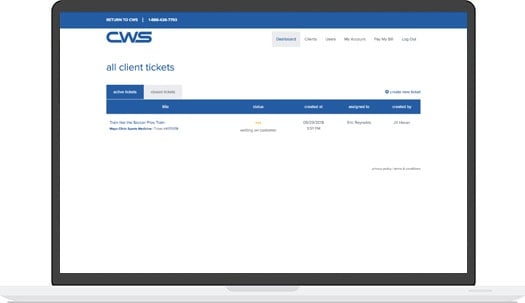 Support Portal
Support Portal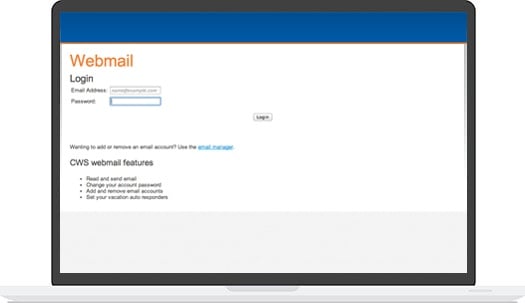 Webmail
Webmail Rapid Newsletter+
Rapid Newsletter+ eCMS
eCMS