
As computers and web-based software have become deeply integrated into our daily lives, so has a consciousness of security issues and the...
Continue reading →Join thousands of other marketers, business owners, and future thought leaders subscribed to our newsletter.

As computers and web-based software have become deeply integrated into our daily lives, so has a consciousness of security issues and the...
Continue reading →Every so often I receive a call from my brother about his computer. You see, he has one of those "technically challenged" personalities. He can tear...
Continue reading →This checklist includes tips, resources, and a checklist for designing a keyword strategy, improving your meta titles and descriptions, and working with on-page optimization. It is designed to get your blog and web content further up on the search engine results food chain!
Security firm Symantec and the Indiana University School of Informatics have discovered a new type of security threat that could leave up to 50...
Continue reading →It has come to our attention that a handful of hosting customers recently received a fraudulent email message claiming to be from CWS. The subject...
Continue reading →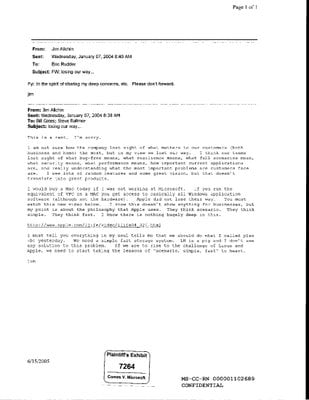
From the class action "Comes et al. v. Microsoft" suit, some very enlightening internal Microsoft emails have been made public. Emails to and from...
Continue reading →

